STMBUGSHIELD
Continuous Cyber Security
With the “Continuous Penetration Test Methodology” of the systems, it is aimed to detect emerging vulnerabilities quickly by testing them by different security researchers at the time intervals determined by our clients. The detected vulnerabilities are subjected to a two-stage approval process, and the verified findings are sent to the client with instant notifications. In this way, the time between finding and removing the vulnerability can be shortened.
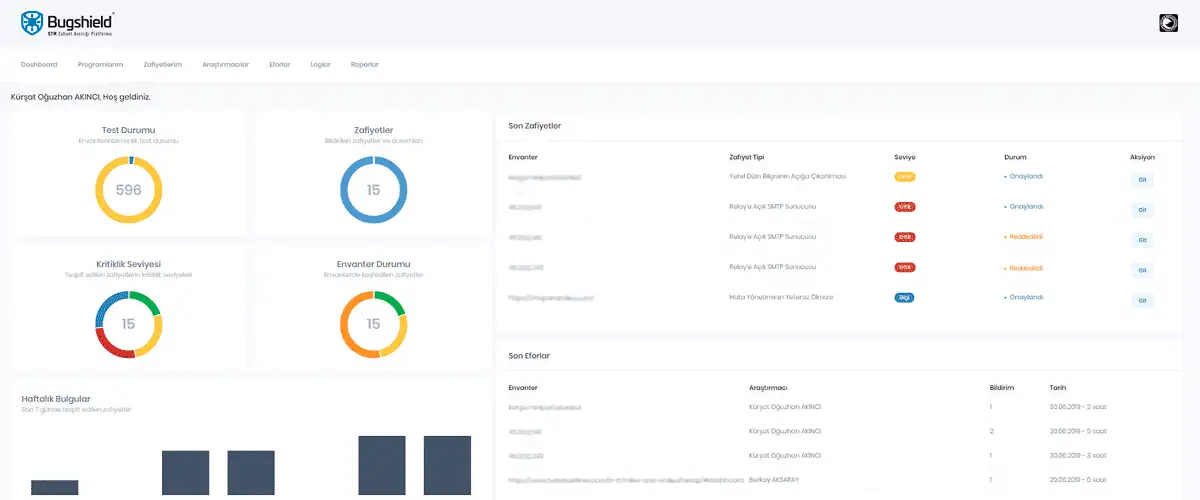
The test status, detected vulnerabilities, severity of vulnerabilities, mitigations against vulnerabilities and the vulnerability inventory can be monitored through the portal. Institutions can request vulnerability research by determining inventory lists and test policies.

Test Status:
Screen displaying the inventory being tested or scheduled for future testing.

Vulnerabilities:
Screen displaying the vulnerabilities detected at the following levels: critical, high, medium, low, information.

Severity Level:
Screen displaying the vulnerabilities detected at the following levels: critical, high, medium, information.

Inventory Status:
Screen displaying the number of domains, IP adresse sor mobile applications where vulnerabilities were detected.
Outstanding Features
- Trustworthiness: Identification of vulnerabilities by a reliable group of researchers who have signed a confidentiality agreement
- Quality: Multiple researchers looking at inventory and checking and verification of detected vulnerabilities by STM analysts
- Agility: Sending instant notifications and taking action for all identified vulnerabilities
- 7/24/365: Conducting tests at more frequent intervals, as opposed to periodic penetration tests